in the cheap vps environment in malaysia, how to ensure data security is a concern of many small and medium-sized enterprises and individual webmasters. this article focuses on practical and executable security measures, with the goal of maximizing risk reduction and compliance under cost constraints, and helping you establish a solid security foundation.
choose the right vps provider and computer room location
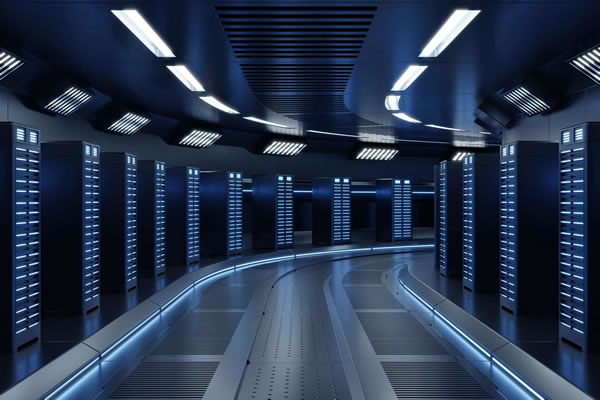
at the procurement stage, it is necessary to pay attention to the supplier's reputation and computer room compliance, and give priority to providers with clear service terms and data center physical and network security measures. pay attention to whether the computer room has redundant networks and backup power, and whether it supports the security features and legal compliance requirements you need.
basic system and account hardening strategies
turning off unnecessary services, disabling direct root login and enabling key-based ssh authentication are basic steps. establishing strong password policies, limiting account permissions, and regularly reviewing user lists can significantly reduce the risk of brute force attacks or permission abuse.
network protection and perimeter strategies
restrict port access using host firewall rules (such as iptables/ufw), combined with ip-based access control and rate limiting. deploy intrusion prevention or simple anti-brute force tools to block common attacks while keeping management interfaces open only to trusted networks or vpns.
data encryption and secure backup solutions
disk or file-level encryption for data at rest and tls/https for data in transit. develop a regular backup strategy and store backups off-site or in a trusted backup service to ensure that backups are recoverable and integrity-verified.
timely updates and patch management
keep security patches on the operating system and key services applied in a timely manner, and prioritize high-risk vulnerabilities. you can use controlled automatic updates or scheduled maintenance windows to ensure backup and rollback plans before and after updates to reduce the risk of accidents.
logging, monitoring and intrusion detection
centrally collect system and application logs and set alarm thresholds to quickly respond to abnormalities. deploy simple intrusion detection or behavior analysis tools to help detect abnormal access and suspicious behavior before passive leakage.
access control, rights management and compliance
follow the principle of least privilege and use role separation and multi-factor authentication (mfa) to improve management account security. comply with relevant data protection regulations and privacy requirements based on the nature of the business, and record necessary audit trails for compliance inspections.
summary and suggestions
ensuring data security in a cheap vps environment in malaysia requires parallel advancement in many aspects including procurement, system reinforcement, network protection, encrypted backup, monitoring and compliance. prioritizing the implementation of basic protection and recoverable backup strategies, combined with continuous monitoring and regular drills, can significantly improve overall security within a limited budget.

- Latest articles
- Risk Tips Hong Kong Station Wolf King Group Information Security And Compliance Concerns
- Cloud Computer Malaysia Server In-depth Evaluation Latency And Compatibility Practical Sharing
- Tariffs And Traffic: Korean Native Ip Card Package Selection Suggestions And Traffic Management Best Practices
- Customer Cases Hong Kong Server Room Introduction Typical Industry Deployment And Performance Optimization Experience Sharing
- Getting Started Guide What Does Hong Kong Native Ip Mean And How To Purchase And Verify The Source?
- Vietnam Server Reliable Website Evaluation Dimension Security Stability And After-sales Service Analysis
- Comparative Analysis And Cost-benefit Assessment Of Pure Hong Kong Cn2 And Traditional Lines
- Community Culture Interpretation Of The Origin And Member Characteristics Of The Hong Kong Station Wolf Pack
- Steps To Deploy Vietnam Cn2 Vps From Scratch And Analysis Of Common Problems
- Summary Of Operational Suggestions For Risk Control In Malaysia Tk. Can Vps From Other Countries Be Used?
- Popular tags
-
Construction Process And Precautions For Malaysian Cloud Servers
This article introduces in detail the construction process and precautions of Malaysia's cloud server, helping you better understand the configuration and management of cloud servers. -
Malaysia Cloud Server Selection Guide And Advantage Analysis
This article provides you with a guide to selecting a Malaysian cloud server and an analysis of the advantages of your choice, helping you make informed decisions in many services. -
Which Vps Is The Best In Malaysia? Must-read Reviews For Users
this article analyzes the pros and cons of vps in malaysia and helps users choose the most suitable vps service.